View
Sorting
Products found: 3038
11th floor Software Development
1Password Manager
- Master Password. Not just the password you use to unlock your vault, it also plays a key role in encryption. Only you know your Master Password.
- Secret Key. Also a star player in key derivation, this unique 128-bit identifier is generated locally. Only you have your Secret Key.
- Secure Remote Password. A zero knowledge protocol that encrypts all traffic over the network. It also verifies the authenticity of the remote server before sending your information over TLS/SSL.
- Tamper-proof, authenticated encryption using AES-GCM mode
- Brute force protection using PBKDF2-HMAC-SHA256
- Secure vault sharing using asymmetric cryptography
- Key creation, derivation, and splitting techniques
247 Labs Software Development
We Specialize In Web Development Full stack, front end, back end, servers, APIs, Android, iOS, Windows, Mac, Linux, Ubuntu Phone. We have the experience and skills to build it right, the first time. We also take on failed projects and bring them back to life. Mobile Apps Mobile application development using cross-platform and native solutions. Support for iOS, Android, watch and TV apps. Integrating mobile devices with other technologies like bluetooth, geolocation and face recognition. Ecommerce Subscriptions, coupons, bookings, conferences, events, SaaS. From the Buy button to your bank account, we can connect all the pieces to allow you to analyze, track and focus on conversions to maximize your online sales. What Makes Our Solutions Standout: Creative Design User experience, interactions, wireframing & mockups. From online to print, complete brand development or mocking up your application idea, we work with your vision and turn it into a complete digital reality. Custom Applications Need a custom application for a startup idea or a business workflow optimization. We take your requirements and help you through a procedure to develop the app into a real working solution. Quality Assurance Test plans, test cases, automation, fault analysis, performance, stability, regression, stress. Quality doesn’t happen by accident, especially in software. We will help you deliver a quality product to the marketplace every time. Product Management Requirements gathering is an essential part of every software development project. We take you through brainstorming, workflow creation, user roles definition, wireframing and clearing defining your solution needs. Project Management A delicate recipe of agile, scrum, lean and water-fall project management methodologies. Our PM process helps eliminate risk from software projects and deliver excellence on time and below budget. Support Your working solution needs ongoing features development, tweak support, bug fixes and maintenance. Our team is there for your around the clock to help with support & provide recommendations to improve your digital needs.
24translate Translation memory systems
- Eliminates double translations, leading to greater efficiency: Translators focus on 'new', previously untranslated text segments.
- Saves the customer time and money: Translations can be delivered more quickly and at significantly lower rates.
- Quality assurance: Consistency with regard to content and terminology is maintained at all times.
2Event
Basic functionality
- Landing Page for your event: get a ready-made "landing page"
- Simple registration of visitors via mail or social networks
- Purchase tickets directly from your smartphone, with a minimum commission of 2.5%
- Ticket and face scanners in smartphone: put an unlimited number of volunteers at the entrance with regular smartphones for control
- Schedule and questions to speakers on the user's phone. In addition to interactivity, this is also saving on printing
- Push notifications: send instant messages to your guests' smartphones with information about schedule changes, promotions or announcements of your next events
- Polls, polls and contests, QR quests: get feedback, hold contests and sweepstakes from partners, engage your audience
- Badges with QR: create your own ticket / badge design and use at your events
- Analytics: get access to full event statistics 24/7, connect Google Ads and track conversions
Networking
- List of visitors in the application and on the website. It can be seen who else will go to the event
- Meetings: scheduling and scheduling meetings between event attendees
- Correspondence between event participants: private and general chats, the ability to ask questions to speakers
- Chat for the projector (Twitter Wall): a large screen on the wall, where posts of event visitors and all posts from social networks with the # hashtag of your event are broadcast in real time. Twitter Wall is one of the visitor attention centers and additional advertising space for sponsors
Advanced networking
- Fellow travelers by car / taxi: visitors create groups by car / taxi or join existing ones to save money and get more time for communication
- Travel Companions Between Cities: Scan your transport ticket and find out who else is someone from your city traveling to the same event in your carriage. This way you will find fellow travelers and meet like-minded people on the road.
- Search for roommates among event participants: reduce living expenses, meet visitors from other cities and spend the night with them
- Geolocation: look at the location of the event participants on the map. An indispensable feature if you are in an unfamiliar city
2muchcoffee Software Development
360Learning
This Collaborative Learning platform relies on peer learning where anyone can elevate and respond to requests for knowledge, closing skills gaps faster. With it’s iterative training framework, minimum viable courses are shipped quickly and improved constantly by peers who identify out-of-date content or suggest additions.
Feedback & data from interactions within the course are also pushed to coaches on the platform, who facilitate peer learning by ensuring that courses are easily accessible, actionable & impactful. From onboarding new employees to training sales reps on a new product pitch, 360Learning aligns employee aspirations with organization expectations.
Overview of 360Learning benefits
360Learning Collaborative Learning platform reduces the feedback loop between expert & employee with lightweight reactions and qualitative forums for asking experts questions while allowing L&D to identify where courses are working and where they need work.
L&D leaders spend less time monitoring course completion (360Learning courses have a 90%+ completion rate) and more time demonstrating business impact.
With build-in Salesforce integration, L&D teams connect the dots between training & time-to-first deal, while our analytics dashboard tracks employee progress - giving them a nudge when they’re falling behind!
With HCM & TMS integrations, 360Learning enables you to evolve on top of our robust platform as an orchestrator of continuous learning throughout the organization.
Thanks to the dedicated sales enablement features, sales trainers using 360Learning to train their new reps also see great results:
- 15% increase in quota attainment
- 30% decrease in ramp up time
- From $500k to $3m in yearly onboarding savings
Level up your sales team with 360Learning's Collaborative Learning Platform. Fast track new hires. Reps hone their script 10x faster with our digital role-play tool. Leverage your team's best examples. Continuously upskill your reps. Co-create impactful courses in just a few hours. Make them available at the point of need through our Salesforce connector and mobile app. Skyrocket sales performance: Demonstrate the impact of training on quota attainment through CRM integration.
360Learning is a learning engagement and training platform that provides learners and trainers with a commonplace to create a learning culture. It allows users to setup digital learning culture in less time and enables them to create online courses in just a few clicks. The platform uses social interaction, gamification and mobile friendly features to get learners engaged and involved in online courses. For trainers, it works more like a marketing and management platform and offers course optimizations, A/B testing and real-time tracking. The platform is being used by some key industry players that all aim to create a global digital learning culture within the organization. It allows trainers and experts to achieve more in less time and helps them become digital experts without having to go through lengthy technology lessons.
- For Trainers and Experts
The platform is compatible with all web and media formats and allows organizations to reuse their existing resources. This allows businesses to leverage their existing best online content and helps them discover innovative formats that make it easier to produce new interactive content. The platform allows creating different kinds of evaluations, including open-ended and closed-ended questions. Trainers can also develop brainstorming sessions, business goals, collaborative activities, exams and more. Trainers and experts can be reviewed by the community, while the platform highlights such reviews to encourage participation. The platform uses a gamified ranking system, which makes it easier to identify top performers for each skill. Advanced tools promote continuous improvement by generating actionable suggestions for course improvement.
- For Learners
360Learning involves learners in online courses on a day-to-day basis and helps increase engagement rates using gamification methods, which are inspired by popular web practices. Groups can be created based on different variables such as by class, by arrival date or by theme, while detailed analysis on these groups or communities can also be performed. The platform puts human interaction at the center of the training strategy by allowing effectively collaborating and innovating during the courses. All the features the platform has to offer are mobile friendly, which allows learners to access important stuff right from their mobile devices, and from anywhere.
3Ants
- DETECTION. 3Ants has advanced and innovative software and processes specifically designed to protect your property and content from piracy.
- ANALYSIS. 3Ants' software and team of experts studies the gathered data and offers specialziaed feedback to the processes so you have more sophisticated content protection methods.
- DELETION. The tools 3Ants uses and its team is fully capable of deleting the links and the pirate content that put your intellectual property at risk.
- Brands and companies. We prevent the dishonest use of your brand by watching over your online reputation. With innovative methods, we protect your brand's image and the use of your identity to improve your consumers' opinion of you.
- Digital contents. We offer content protection of the best quality by removing the illegal copies and unauthorized sharing. We also redirect the user to legal pages where they can purchase your product or find information on it.
- Physical Products. We work to increase and protect your legal sales, as well as to eliminate forgeries in online sales.
3D Warehouse
A community for all Anyone can search, download models from, and contribute content to 3D Warehouse, for free. The world’s largest 3D content platform features direct integration with SketchUp Pro and compatibility with CAD apps.
Sharing is caring Not every model in 3D Warehouse has to be shared; private items are accessible only to you. Public models can be searched and downloaded. Models can be organised into collections and shared to social media.
Content marketing platform 3D Warehouse offers product manufacturers a unique way to showcase catalogs, allowing prospects to specify product into their own designs. The 3D model is a native channel to reach and engage new customers.
Certified content development SketchUp has built a strong network of Certified Content Developers; together they are equipped to build professional models for those organisations seeking to get their content noticed on 3D Warehouse.
3DEXPERIENCE platform
6Connex Platform
6Connex is a virtual platform like no other — with the robust flexibility needed to create any interactive environment in the cloud. You have the ability to power fully-remote and hybrid events for Marketing, Sales, HR, Business Development, and more.
Attendee-centric experiences
Attendees can easily interact with advanced engagement tools, such as 1:1 chat, video chat, gamification, social sharing, and webcasting, while leveraging our sophisticated A.I. technology that allows for a unique, personalized event experience with content-matching and networking opportunities.
Enterprise-level security
As the virtual event industry’s leader in security and privacy, many of the world’s most admired companies have put their trust in our security and privacy protocols. We comply with the most stringent enterprise security requirements with features including whitelisting, blacklisting, and secure cookie handling.
Actionable insights
Track activity and ROI with 24/7 access to 35+ real-time reports. Understand the Who, What, Where, and When for every activity in your virtual environment. Provide your sponsors with actionable data that allows them to target campaigns accurately. Key features of 6Connex: Unmatched Scalability with Enterprise Level Security The 6Connex platform is ISO 27001 certified, offering a secure virtual environment with unlimited capacity and flexibility to host any hybrid or virtual use case.
The Perpetual VE Concept
The 6Connex platform handles multiple use cases, allowing customers to repurpose the Environment and leverage their long-term license to support multiple engagements in a single location.
Immersive Experience
Our environment templates and navigation design drive attendees through a unique immersive experience, delivering a new level of engagement and virtual experience.
Open VE Universe
6Connex’s platform is technology agnostic allowing clients to bring the tools they use day-to-day and are approved by their IT protocols to integrate with our platform and drive engagement.
6Scan
What Does 6Scan Do?
- Find. The 6Scan six independent scanners work to detect vulnerabilities, scan for malware and inspect your website's files to determine any security issues or risks.
- Fix. Patent-pending technology automatically fixes any security issues as soon as they are detected. We deploy a WAF (Web Application Firewall) and custom vulnerability patches to make sure any attack vectors are blocked. The entire process of detecting and fixing vulnerabilities is fully automated, managed through a unified dashboard.
- Protect. 6Scan will continue to monitor your site for new vulnerabilities and security risks. The scanning is scheduled automatically or can be triggered manually and you will be notified of any issues. As with all our services, this process can be monitored from your dashboard where you have the opportunity to roll back any changes.
7devs Software Development
- constantly growing and expanding functionality;
- scalable infrastructure;
- redesign according to the latest trends;
- clean code and its maintenance during the whole process of our collaboration.
802 Secure AirShield
8allocate Software Development
A-listware Software Development
A10 Thunder® ADC
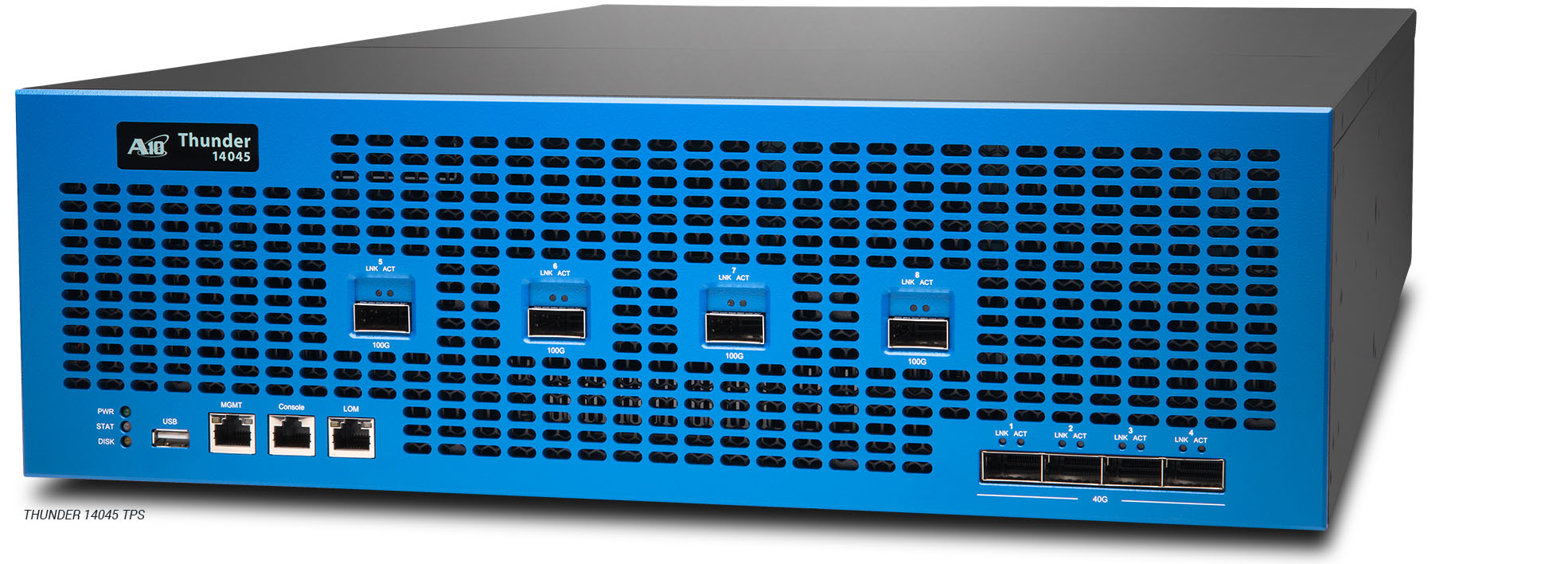
A10 THUNDER®TPS
AB Soft Software Development
- We have built the platform for our product from scratch utilizing cutting-edge technologies.
- Our product is a market leader with over 270 000 business customers and growing.
- We provide high load 24/7 service with 99.999% availability.
- We have great team of dedicated professionals and are always on lookout for new talents.
- PHP
- Java
- HTML5+CSS3
- JavaScript/jQuery
- Python
- C/C++
- Mobile development
- Flexible working hours
- 4 weeks of paid vacation
- Medical insurance and paid sick-leaves
- Fully paid English classes and own library
- Comfortable office facilities (kitchens, coffee and tea, sweets, fridge and microwave, gyms, own parking, table tennis, kicker, billiards etc.)
- Sport activities (training tennis, yoga, basketball and soccer teams), state holidays celebration and corporate events.
Abatis for Maritime ICS SCADA
- Communication Systems
- Bridge Systems including ECDIS
- Propulsion & Power Control
- Access Control Systems
- Cargo Management Systems
- Passenger Servicing & Mgt.
- Passenger-facing Networks
- Core Infrastructure Systems
- Admin & Crew Welfare Systems
- Proactive Protection
- No Updates Required
- Fast
- Safe
- Efficient
- Low Power Consumption
- Evaluated Extremely Small Footprint (<100KB)
- Fit-and-Forget
- Protects Legacy and New Operating Systems Can Identify and Isolate Existing Malware Infections
- Works with Existing Security Tools
- Easy to Use Reduces Maintenance Burden
- Improve Green Credentials through Energy Saving
- Ship & Shore Capability
The ROI4CIO Product Catalog is a database of business software, hardware, and IT services. Using filters, select IT products by category, supplier or vendor, business tasks and problems. Find the right business solutions by using a neural network search based on the results of deployment products in other companies.